Pegasus, of late known as government spyware, has created a stir in the minds of people all around the globe. The company has accepted that they sold the software to 40 countries or governments. Even if your country is not a subscriber still there are chances that the enemy nations may use it against you since the mobile phones are part of a wider network. Once such software falls in the hands of wrong people, they can use it against one and all, at free will, without following any laid down principles.
Business sector also needs to be careful with their cell phone usage since the same software can be used to extract vital info from your company for the benefit of any sort of end users including competitors, tax collector and more. Ideally, the software like Pegasus is a good tool for Market Research and Market Intelligence agencies to understand the consumer behavior, if it can be legalized for the same purpose under controlled conditions.
Per the news report, Pegasus has the technology to infect a device across miles away. Once a device has been infected, it begins duplicating messages sent or received from the target phone, harvesting photos of the target, and secretly recording the surroundings by turning on the camera and activating the microphone to listen in on the conversation. Finally, it can track a target using the GPS feature. It can monitor where the target is, where the target has been, who the target meets, and what the target talks about.
Another, dangerous method of attack is to use a BTS (Base Transceiver Station), also known as a “rogue cell tower,” “IMSI Catcher,” or “stingray,” which impersonates legitimate cellular towers and forces mobile phones within a radius to connect to them, allowing an attacker to manipulate the intercepted traffic. In November 2019, a New York City-based tech reporter captured an intercepting gadget on exhibit at Milipol, a homeland security trade event in Paris. When it comes to BTS attacks, the user has little recourse; it is up to law enforcement and network service providers to be vigilant against the BTS.
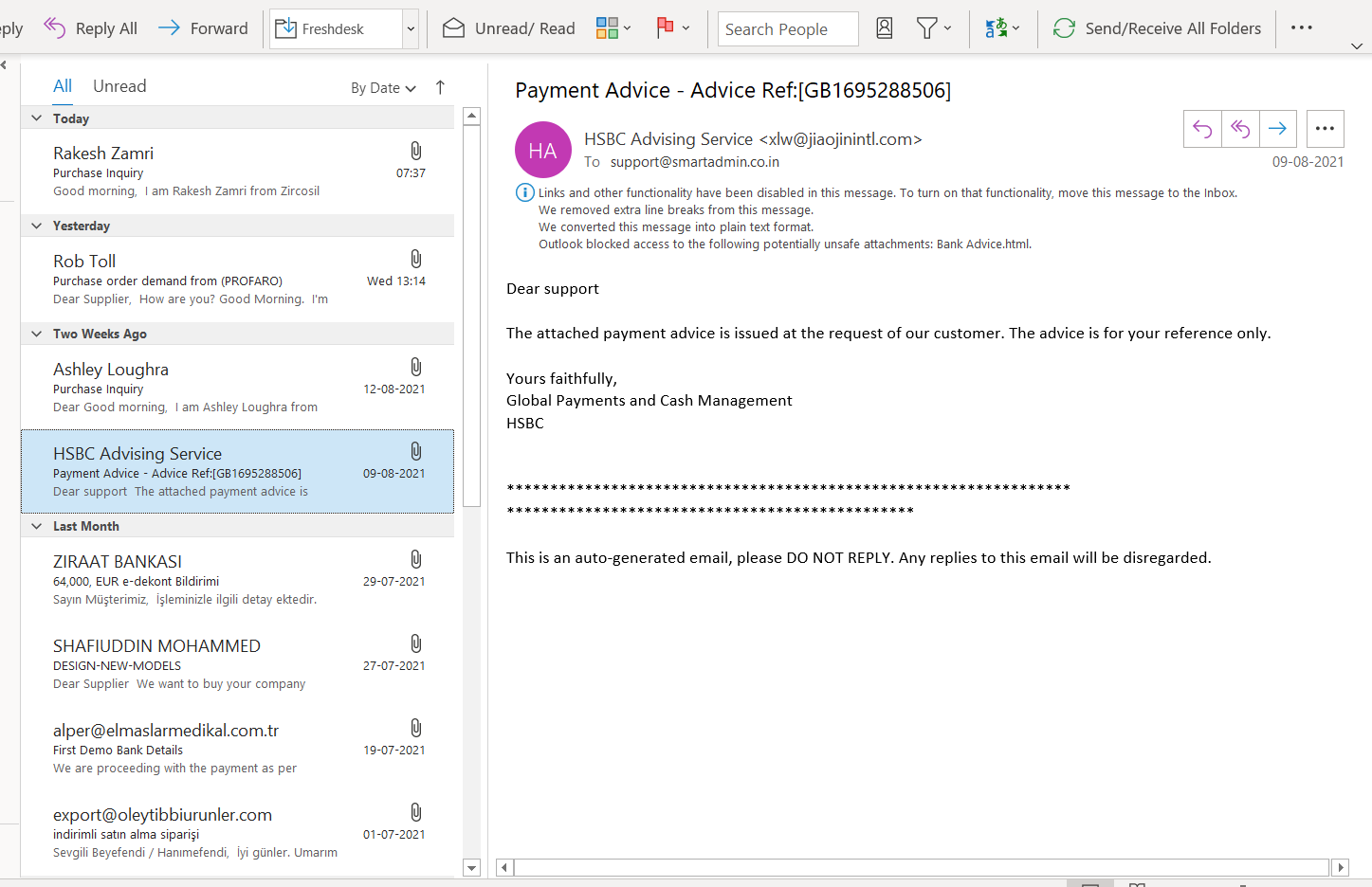
Now, it is not the question about the Pegasus for general users. Anybody with good technology knowledge can create a Spy software, or another Pegasus. It has been in the market, as we see from the many unknown emails and messages which say “your invoice is paid”, “notice from tax authorities”, “notice from court”, “Your DHL Parcel arrived” “you won a lottery” and more. Thus, overall, there is a sense of insecurity among all types of cell phone users which raised two very common questions now.
- Is my phone safe?
- And how can I secure my phone and data against any spyware, not just Pegasus?
The answer to the first question is simple:
Almost any mobile phone linked to a network is susceptible to spyware.
Before addressing the second question, some misconceptions about spyware need to be dispelled.
COMMON MYTHS
- i-Phone users assume their operations are entirely secure.
Fact: i- Phones are commonly accepted as the most secure phones, but its most secure feature makes it more vulnerable. This is for two reasons: first, the high security the operating system provides intimates hackers to exploit the vulnerabilities, and second, the operating system is primarily used by journalists, diplomats, business leaders, and politicians, who used to be the target for spying
- Phones with “end-to-end encryption” will not be protected.
Fact: The term “end-to-end encryption” refers to the security of data transfer between devices. Because the message is encrypted with a particular key, it may be used to prevent “man-in-the-middle” attacks, in which a hacker intercepts communication between its originator and receiver. However, it is ineffective against “endpoint” similar to Pegasus software.
- Spyware can’t infect all devices.
Fact: Irrespective of the operating system (Android, IOS, Microsoft, and Fire), different operating systems give different layers of security, but they are always prone to Zero-Day vulnerability.
- Spyware is intended to operate invisibly and conceal its traces.
Fact: Pegasus model attacks proved that it can be performed remotely from any country. The spyware attacks are detectable with thorough forensic examination. There is no software or antivirus to keep the phone from being infected; in fact, some badly designed antivirus applications may convert the phone into a vulnerability.
What All PREVENTIVE MEASURES Now?
Some preventive measures can be taken to protect mobile phone against infection. It will help to reduce the likelihood of phones being infected in the first place, but there is no guarantee of protection. Here below a type of spammy messages to source your email access in your inbox.
As a rule, our effort should be to avoid infection in the first place. Here are a few tips which can be done without using much technology to prevent the infection in the first place. Almost like “Wash your hand frequently” and “Keep a distance of 2 meters”!
- Do not click on unknown links, strange and odd communications with a link, mainly if it contains a feeling of urgency, such as “you have won a million dollars, please click the link”. Also, avoid clicking on “shortened links” which we do not know until it is opened
- Use proper browsers, set browser security to medium and think carefully before entering any personal or sensitive information.
If need one can go for high-quality anti-malware software and keep the system updated and scanned regularly. However, so far, no anti spying software found in the market.
Here is a list of potential ways that the device may get infected and information on how to mitigate them.
- Zero-day Vulnerability-Hackers often attack zero-day vulnerabilities, – There are faults or defects in an operating system or application that the manufacturers or developers are unaware. In 2019, WhatsApp was a victim of this vulnerability, with over 1,400 phones affected. Malicious programs may be placed on a target device simply by making a WhatsApp call, even if the victim never answers the call. Similarly, Apple’s i Message became a victim of a similar flaw, allowing it backdoor access to hundreds of millions of iPhones. When it comes to Zero-Day Vulnerabilities, mobile phone developers and application developers have most of the burden of protecting against Spyware infestation.
However, users may also take precautions to minimize risk, such as listed below;
- Reduce the number of applications on your phone; fewer apps imply fewer virtual doors for an attacker to exploit. Try to keep the number of apps needed to conduct day-to-day tasks to a bare minimum. There are certain applications that are integrated into the system that the user cannot uninstall. Please be aware that most of the mobile apps have root or admin access or they seek such access while installation
- Review the installed applications regularly, verify their permissions and consumption, and uninstall any you no longer need. The iPhone user may restrict the application’s capacity to track by utilizing an inbuilt security setting. By doing so, insecure apps can be handicapped.
- Regularly update both the phone’s operating system and individual apps since updates close vulnerabilities.
- Avoid downloading applications from untrusted sources, specifically on Android phones. avoid installing applications through the API’s
- When you download software, be sure to read the end-user license agreement before proceeding with the installation. If you are unsure, do not install the software.
- It is also possible for spyware to infect a phone by intercepting network traffic using a man-in-the-middle (or MITM) assault, in which the attacker intercepts unencrypted network traffic (such as HTTP web requests) and redirects it to malicious payloads and this is beyond the control of users
- Use a VPN on both your desktop and mobile devices as an alternative. All connections are securely tunneled to the VPN server, which then visits websites on your behalf and transmits them back to you. However, when using a VPN, it is necessary to know that the VPN service provider can spy on your internet traffic, so choose a reliable one.
DART Consulting provides business consulting through its network of Independent Consultants. Our services include preparing business plans, market research, and providing business advisory services. More details at https://www.dartconsulting.co.in/dart-consultants.html